(Just to let members know that we are now offering help to the Neston and Willaston Primary Care Network (PCN) - Allen Roochove, NCCC Techno Buddy 09.09.24)
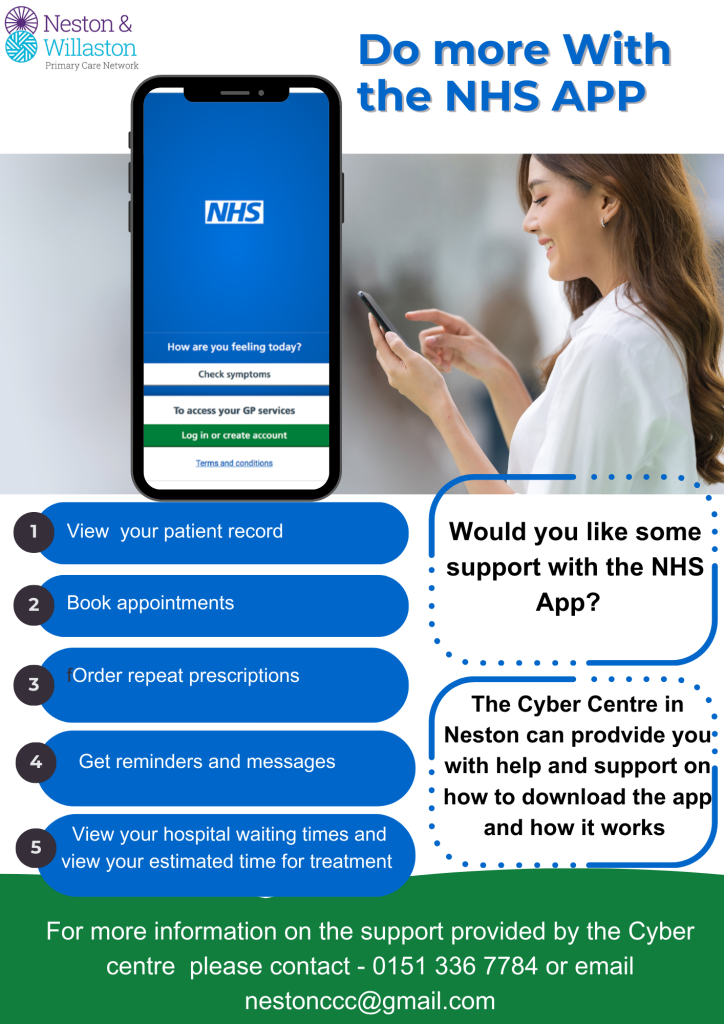
Did you know that the NHS App allows you to order your repeat prescriptions, book appointments, and a range of other things?
Would you like some help with how to download the app and how it works ?
The Cyber Centre in Neston offers drop in sessions every week to offer support and guidance. For more information about these sessions please contact the centre on 0151 336 7784 or email them on nestonccc@gmail.com
Also, here's a link to the Neston and Willaston PCN website
https://nestonwillastonpcn.com/
----------------------------------------